Expedite Ransomware Detection to Minimize Impact
When prevention fails, Progress® Flowmon® helps detect early indicators of ransomware attacks using a combination of AI, signatures and threat intelligence to help customers respond with greater confidence and clarity.
Launch demo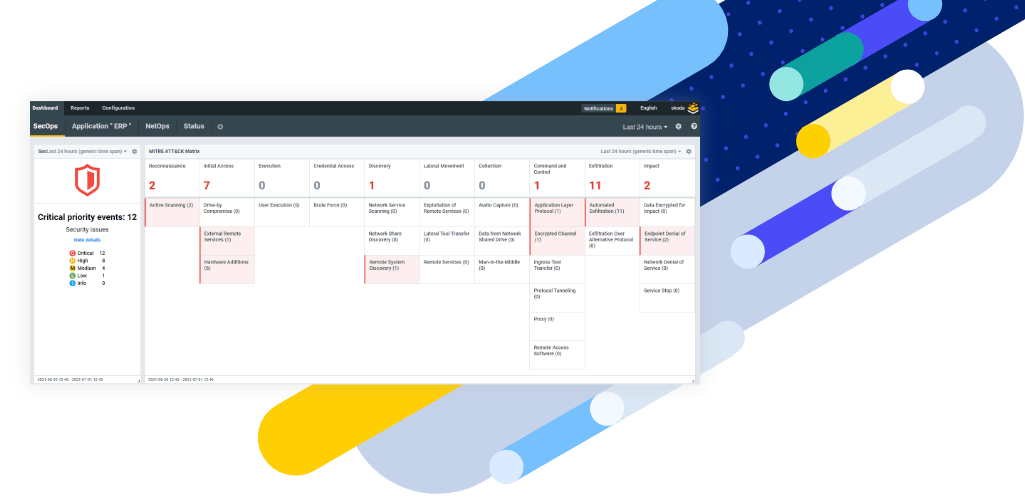
Minimize Blind Spots to Reduce Impact

Advanced AI-Powered Analysis
Expedite detection of both known and zero-day ransomware attacks, reducing the risk of significant data loss and financial impact.

Automated Response and Mitigation
Minimize the need for manual intervention, reducing response time and limiting the potential damage of an attack.

Superior
Performance
Leverage up to 6x higher performance than competitors, minimizing missed ransomware threats for more reliable security.

Scalable
Coverage
Scale your detection to cover east-west traffic and minimize blind spots in both on-premises and cloud environments.
Help Mitigate Ransomware Attacks
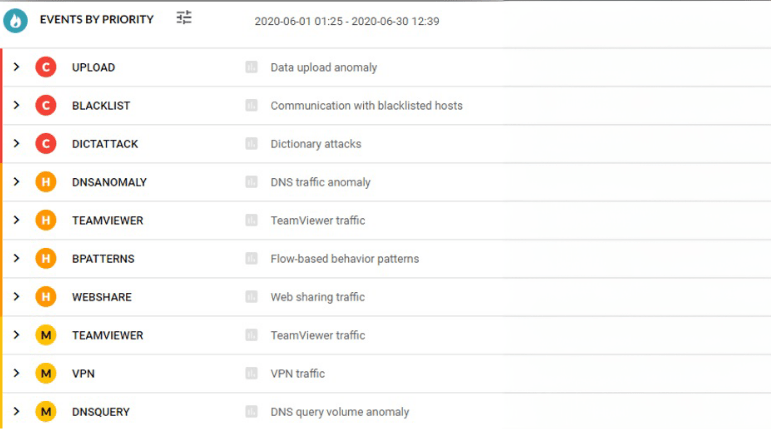
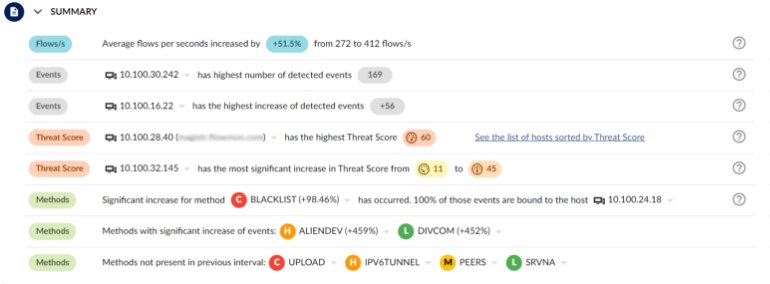
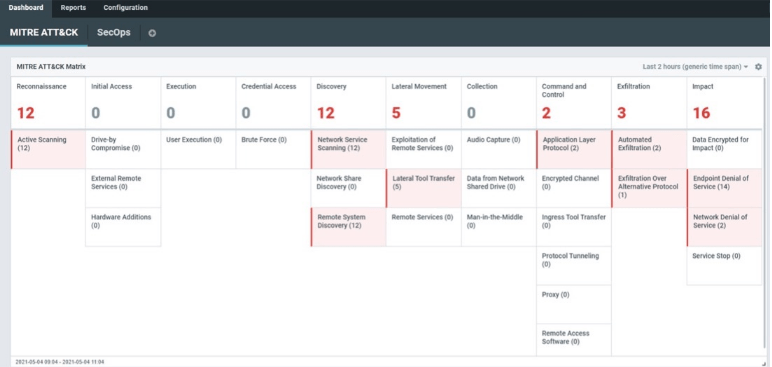
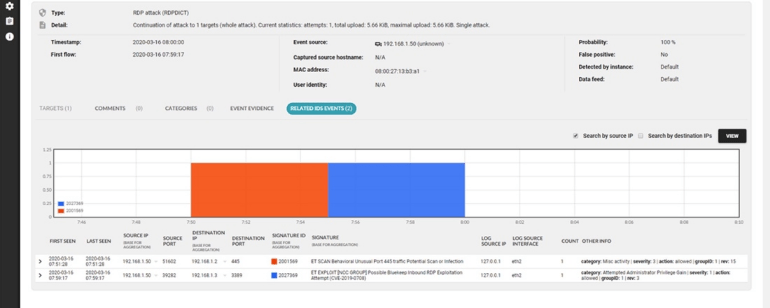
Unlike traditional security approaches, Flowmon combines the precision of signature-based detection with the adaptive learning capabilities of AI, enhanced by the extensive insights in global threat intelligence. This synergy creates a dynamic, multi-layered protection mechanism—hardening IT environments against both known and emerging ransomware threats.
| Flowmon NDR + IDS engine | Traditional IDS | |
|---|---|---|
Typical Deployment | Network Wide | Network Perimeter |
Signature-based Detection of Known Threats | ||
External Attacks | — | |
Insider Threats | — | |
East-west Coverage | — | |
AI Detection of Unknown Threats | — | |
Enterprise-grade Threat Intelligence | — | |
Native Cloud Support |
Reveal ransomware before it is too late
Spend less time investigating and improve your response times with Flowmon’s powerful features.